Understanding the Fundamentals of Carbon Black EDR Architecture: A Comprehensive Guide
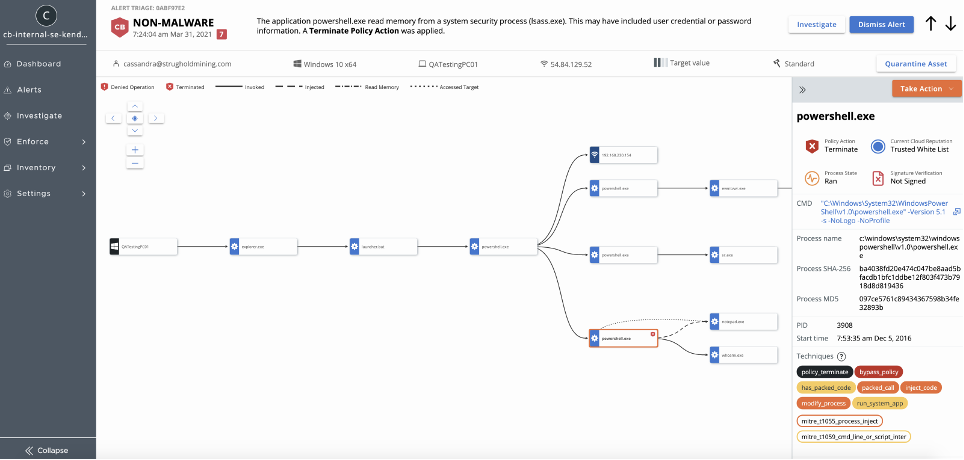
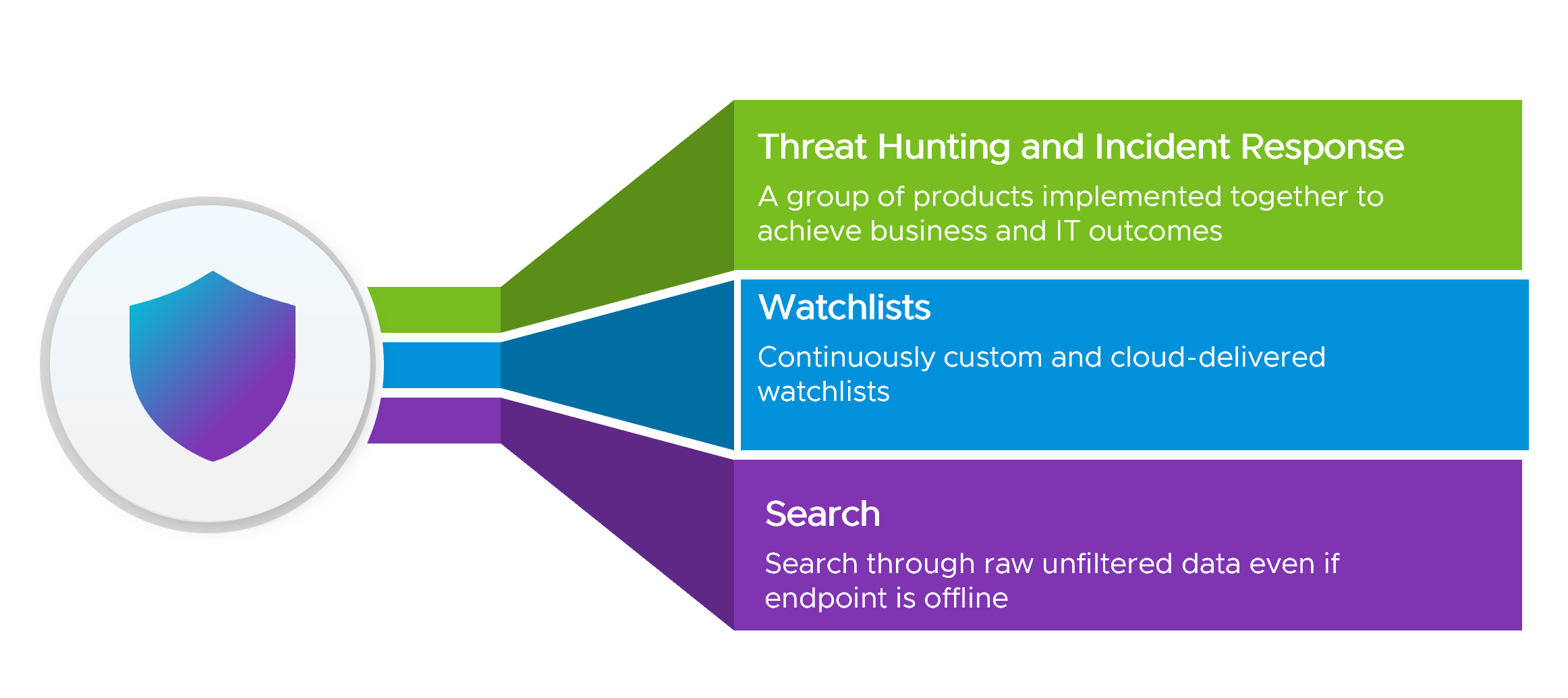
In any organization, security is of paramount importance. Carbon Black EDR (Endpoint Detection and Response) is a security solution that offers enhanced protection against sophisticated attacks. It does this by providing visibility into and control over all activity on endpoint devices. In addition, Carbon Black EDR automatically detects and responds to threats in real time, […]
The Ultimate Carbon Black EDR Admin Guide: A Step-by-Step Tutorial for Effective Endpoint Security
Carbon Black is one of the most popular endpoint security solutions on the market. If you’re looking for a comprehensive guide to configuring and managing Carbon Black EDR, you’ve come to the right place. In this article, we’ll walk you through everything you need to know about Carbon Black EDR, from installation to daily administration […]
Boost Your Endpoint Security with Carbon Black Cloud Enterprise EDR
Are you tired of constantly worrying about cyber threats targeting your organization’s endpoints? Look no further than Carbon Black Cloud Enterprise EDR, the ultimate solution to boost your endpoint security. This powerful tool offers a comprehensive approach that identifies and responds to threats in real-time, ensuring maximum protection for your network. Read on to discover […]
EDR Abbreviation in Computer Science
Have you ever come across the abbreviation EDR in computer science and wondered what it stands for? You’re not alone! As a tech enthusiast, understanding industry jargon is important, especially when it comes to cybersecurity. In this blog post, we’ll unravel the mystery of EDR and explore its significance in today’s technology landscape. So buckle […]
Protect Your Network: How Firewalls Defend Against Malicious Attacks?
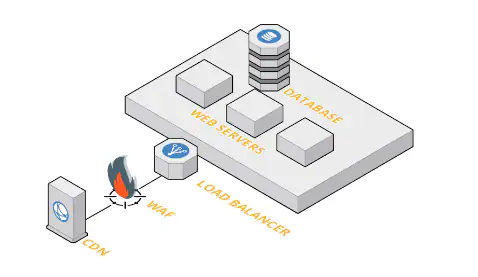
In today’s digital age, security should be a top priority for individuals and businesses alike. With the increasing number of cyber threats, it’s essential to have reliable tools to safeguard your network from malicious attacks. That’s where firewalls come in – they act as a critical first line of defense against hackers and malware attempting […]
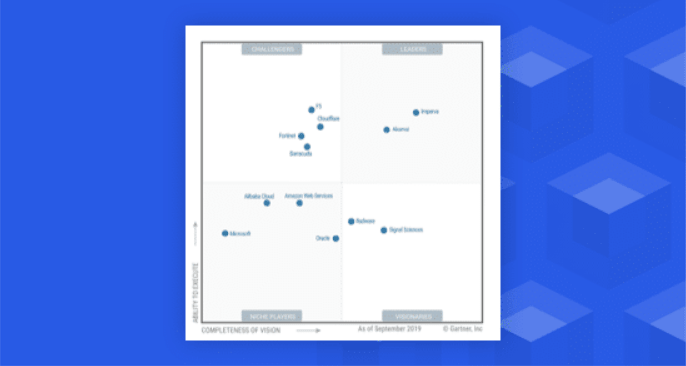
Navigating the Gartner Magic Quadrant for Web Application Firewalls: What You Need to Know
Welcome to the world of Gartner Magic Quadrant, where top-notch web application firewalls (WAFs) are evaluated and recognized for their excellence. If you’re a security professional who’s constantly looking out for ways to protect your organization from digital threats, then this post is definitely worth your time. In this article, we’ll take you through everything […]
Why Your Business Needs a Cloud Web Application Firewall: Protecting Your Online Assets
Are you looking for an effective way to safeguard your online assets? Do you want to protect your business from cyber attacks and data breaches that can compromise sensitive information? Look no further than a cloud web application firewall (WAF). In today’s digital age, businesses of all sizes need robust security measures in place. A […]
Comparing Top Players in the Web Application Firewall Market: Which One is Right for You?
Are you concerned about the security of your web applications? Do you want to protect your business from cyber threats and attacks? Look no further than a Web Application Firewall (WAF). But with so many options in the market, which one is right for you? In this blog post, we’ll compare top players in the […]
How to Get the Most Out of Palo Alto Networks Web Application Firewall Features?
Are you tired of constantly worrying about cyber threats attacking your web applications? Look no further than Palo Alto Networks Web Application Firewall (WAF). This powerful tool provides a comprehensive defense against attacks, but are you getting the most out of its features? In this blog post, we’ll dive into how to maximize the benefits […]
Ransomware and Cyber Extortion: Response and Prevention
Welcome to our latest blog post on the ever-growing threat of ransomware and cyber extortion. In today’s digital age, it’s become increasingly important for individuals and businesses alike to be aware of these insidious attacks that can leave you feeling helpless and vulnerable. From healthcare facilities to small startups, no one is immune from the […]