Search Results for:
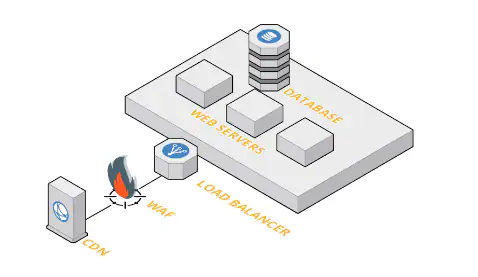
Comparing Top Players in the Web Application Firewall Market: Which One is Right for You?
Are you concerned about the security of your web applications? Do you want to protect your business from cyber threats and attacks? Look no further than a Web Application Firewall (WAF). But with so many options in the market, which one is right for you? In this blog post, we’ll compare top players in the […]
How to Get the Most Out of Palo Alto Networks Web Application Firewall Features?
Are you tired of constantly worrying about cyber threats attacking your web applications? Look no further than Palo Alto Networks Web Application Firewall (WAF). This powerful tool provides a comprehensive defense against attacks, but are you getting the most out of its features? In this blog post, we’ll dive into how to maximize the benefits […]
Ransomware and Cyber Extortion: Response and Prevention
Welcome to our latest blog post on the ever-growing threat of ransomware and cyber extortion. In today’s digital age, it’s become increasingly important for individuals and businesses alike to be aware of these insidious attacks that can leave you feeling helpless and vulnerable. From healthcare facilities to small startups, no one is immune from the […]
Ransomware: Defending Against Digital Extortion
Welcome to our latest blog post on ransomware! As the world becomes increasingly digital, cybercriminals are continuously finding new ways to exploit vulnerabilities in computer systems. One of the most significant threats facing businesses and individuals alike is ransomware – a type of malware that encrypts your files and demands payment in exchange for their […]
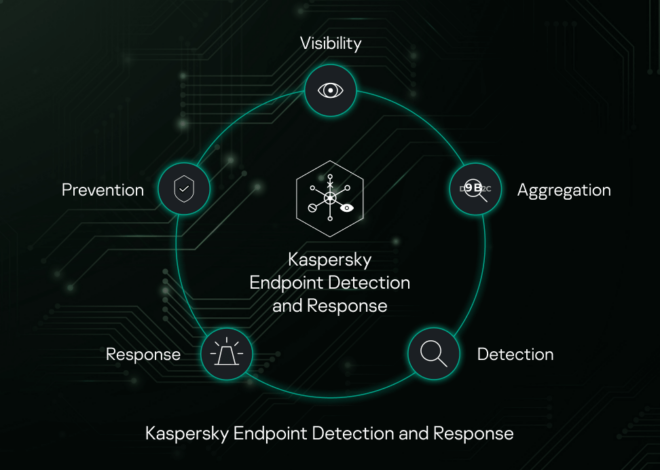
Why Endpoint Detection & Response (EDR) is Crucial for Your Cybersecurity Strategy?
In today’s digital age, cybersecurity is more important than ever before. With cyber threats becoming increasingly sophisticated and complex, businesses of all sizes are at risk of falling victim to a data breach. Endpoint Detection & Response (EDR) has emerged as a crucial component of any cybersecurity strategy that aims to keep hackers at bay. […]
Empowering Your Cybersecurity with Endpoint Detection and Response (EDR) Software
Introduction to Endpoint Detection and Response (EDR) Endpoint detection and response (EDR) software is a type of security solution that helps organizations detect, investigate, and respond to malicious activity on their endpoint devices. Endpoints are the devices that connect individuals and businesses to networks, such as laptops, desktops, servers, and mobile devices. EDR solutions are […]
Privacy Policy
Privacy Policy Welcome to ScanToComputer.com (the “Website”). Your privacy is important to us. This Privacy Policy outlines how we collect, use, disclose, and protect your information when you access or use our Website. By using our Website, you agree to the practices described in this policy. 1. Information We Collect When you visit ScanToComputer.com, we […]
Some Useful Links for You to Get Started
It seems like you’re running a default WordPress website. Here are a few useful links to get you started: Migration How to use WordPress Migrator Plugin? Migrate WordPress from Siteground to Cloudways Migrate WordPress from GoDaddy to Cloudways General How do I take my website live from Cloudways? How to manage WordPress via WP-CLI on […]